Best Online Privacy Tools 2018


Most people know that the issue of ad stalking – known in the trade ‘remarketing‘ or ‘retargeting‘ – has something to do with cookies but that’s barely the half of it.
The underlying tracking for all this is supplied by the search engine provider or one of a number of programmatic ad platforms most people have never heard of. The ad system notices which sites people are visiting, choosing an opportune moment to ‘re-market’ products from a site they visited at some point based on how receptive it thinks they will be.

Almost every popular free service, including search engines, social media, cloud storage and webmail, now gathers intrusive amounts of personal data as a fundamental part of its business model.The service is free precisely because the user has ‘become the product‘ whose habits and behaviour can be sold on to third parties by advertisers and profilers.
Broadband providers, meanwhile, are increasingly required by governments to store the internet usage history of subscribers for reasons justified by national security and policing.But do not fear, for there are some products out there that can protect your data from prying eyes and keep you safe and anonymous online.
VPNS
In theory, the traditional way of shielding internet use from ISPs can be achieved using a VPN provider.A VPN creates an encrypted tunnel from the user’s device and the service provider’s servers which means that any websites visited after that become invisible to the user’s primary ISP. In turn, the user’s IP address is also hidden from those websites.
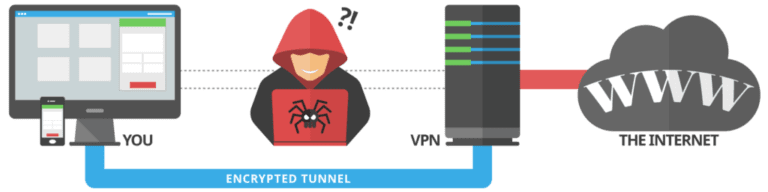
Notice, however, that the VPN provider can still see which sites are being visited and will also know the user’s ISP IP.Some VPNs are free, but they typically subsidise this by serving you pushy ads and putting a time limit on the free plans. Free VPNs also sometimes limit the servers you can connect to or slow down your speeds more than a VPN already does.Good VPNs don’t have to cost the earth. You can pick up a good service for around £5 per month and not have to worry about a bad user experience.
Nord VPN
IPVanish
Cyberghost
PureVPN
ProtonVPN
SPYWARE REMOVAL TOOLS
SUPERAntiSpyware
Emsisoft Emergency Kit
Malwarebytes
Malwarebytes alongside its extensive range of online security tools provides some excellent antispyware capabilities.If you opt for this product, you’ll be able to scan whole hard drives, as well as individual files and folders. And of course, web protection, including detecting and preventing access to malicious sites, ads and scam networks.
PASSWORD MANAGERS
1Password
With 1Password you can store a vast amount of information from account details and passwords to bank details and loyalty schemes and what’s great is that it will auto-fill web forms for you once these are stored.1Password also enables Touch ID which uses your fingerprint for entry, which adds an extra, and useful layer of security.In addition, to make sure all your current passwords are up to code, there is an audit function that will highlight weak passwords and generate stronger ones for you to replace them with.
LastPass
If you’ve been on the hunt for a password manager for a while now, you’ll have heard of LastPass, and with good reason. It really is one of the best out there.Although, that’s not to say that it’s been smooth sailing.

LastPass was hacked in 2015, compromising account email addresses, password reminders, server per user salts, and authentication hashes.Since this, LastPass really has redeemed itself, offering end-to-end encryption at device level, so even LastPass can’t see your passwords.
EnPass
EnPass has a similar interface and set of features to LastPass. The desktop version is free but the mobile app costs $9.99 (£7.80) per platform.The free version includes browser support with autofill functions for Safari, Chrome, Opera, Firefox, and Edge, but the closed source software has no publicly available security audit.
PRIVACY BROWSERS
Firefox
Firefox is by some distance the best of the browser makers for privacy, simply because it does not depend on the user tracking that helps to fund others. But this becomes moot the minute you log into third-party services, which is why most of the privacy action in the browser space now centres
Tor
This Firefox-based browser that runs on the Tor network can be used with Windows, Mac or Linux PCs. This browser is built on an entire infrastructure of ‘hidden’ relay servers. Unlike other browsers, Tor is built for privacy only, so it does lack certain security features such as built-in antivirus and anti-malware software.
Brave
Brave is an open source browser with advanced ad-tracking controls that makes it ideal for the privacy-conscious user who wants a lightweight browser. It integrates with httpsssssS Everywhere, blocks cookie capture, includes a decent ad-blocker, and is regularly improved by an active developer community.
PRIVACY SEARCH ENGINES
It might seem a bit pointless to worry about a privacy search engine given that this is an inherent quality of the VPN services already discussed but a couple are worth looking out for, as they’re free and incredibly simple.
DUCKDUCKGO
This means visited sites will not know what other terms a user searched for and will not be sent a user’s IP address or browser user agent. It also offers an encrypted version that connects to the encrypted versions of major websites, preserving some privacy between the user and the site.
In addition, DuckDuckGo offers a neat password-protected ‘cloud save’ setting that makes it possible to create search policies and sync these across devices using the search engine.
OSCOBO UK SEARCH
DNS NAMESERVERS
Techworld’s sister title Computerworld UK recently covered the issue of alternative DNS nameservers, including Norton ConnecSafe, OpenDNS, Comodo Secure DNS, DNS.Watch, VeriSign and, of course, Google.
DNS.Watch
OpenDNS
Now part of Cisco, the primary is 208.67.220.220 with a backup on 208.67.222.222. Home users can simply adjust their DNS to point at one of the above but OpenDNS also offers the service wrapped up in three further tiers of service, Family Shield, Home, and VIP Home. Each comes with varying levels of filtering and security, parental control and anti-phishing protection.
Cloudflare
PRIVACY UTILITIES
You might also want to look into some privacy apps and software to support other things in the list. You should consider:
Two-factor authentication: Given the amount of data users are storing, using two-factor authentication (2FA) is an absolute must. This can be set up using a mobile app such as Google Authenticator, Authy or FreeOTP.
Backup and Sync: You should sync data across multiple devices in an encrypted state, whether that be with Google or other providers such as Dropbox or Box, for example.






